Securing Your Agency / Security Features in AngelTrack
Suggestions for hardening your mobile fire and/or EMS operation, and explanations of AngelTrack's many security features.
Many initial steps, plus ongoing company policies and enforcement, are required to secure a mobile, paperless operation in today's hostile security environment. Most are necessary for HIPAA compliance, but all are sensible and inexpensive.
This is a Shared Responsibility Model, in which the responsibility for IT security and reliability is shared between:
- AngelTrack,
- AngelTrack's datacenter (Rackspace), and
- The customer.
For a summary of all these items, please refer to the Shared Responsibility Guide.
Role-Based Access Control
 AngelTrack uses role-based access control to grant access to its features and data.
AngelTrack uses role-based access control to grant access to its features and data.
When an employee is a member of a role (such as "dispatcher"), that employee has all the privileges of that role, including read and (sometimes) write access to that role's data. Some roles are very powerful, with write access to large amounts of company data.
Greater access creates greater opportunities for accidental damage. So, do not add employees to any role unless they have a bona fide and ongoing need for those access privileges. Promptly remove them from roles they no longer perform.
Use the Administrator Account Only When Necessary
We strongly recommend never use AngelTrack's built-in administrator account for day-to-day operations. The administrator account has full read/write access to everything in AngelTrack, so a person logged-in as administrator has many opportunities to accidentally modify something important. This is a liability, no matter how trustworthy or careful your employees are.
Furthermore, the administrator account does not have any specific person's name on it. As such, its activities cannot be positively traced to an individual.
Use the administrator account to create yourself a separate employee account. Add yourself to whichever roles you require. Then logout, and log back in using your new account.

Do Not Share Accounts
We strongly recommend that every person who accesses your AngelTrack cloud server have their own separate employee account. No exceptions.
We urge you to resist the temptation to create an employee account named "QAReview" or "Billing" for multiple people to use. When multiple people share an account in that manner, it becomes impossible to tell which one of them performed which action. You won't be able to trace a mistake back to the person who needs retraining.
This also applies to any outside contractors who you invite in to your cloud server. Even if the contractors all operate under a single company ("Acme Billing"), do NOT create them an "AcmeBilling" account even if they specifically request it. It is best if each one of Acme Billing's employees has a separate account in their own name.
Provisional Access / IP Whitelist for High-Access Employees
 The high-access security roles of Dispatcher, Call-taker, Biller, Lieutenant, and Captain can be made subject to AngelTrack's IP whitelist, by marking them ☑ Provisional.
The high-access security roles of Dispatcher, Call-taker, Biller, Lieutenant, and Captain can be made subject to AngelTrack's IP whitelist, by marking them ☑ Provisional.
A provisional employee will enjoy their high access only when they are connecting from an IP address in AngelTrack's list, i.e. only when connecting from a company-owned network. At all other times, they will lose the aforementioned access, but will still enjoy their other access roles.
The provisional setting does not affect user accounts who are marked as Administrator.
To learn more about AngelTrack's security roles, including the Provisional mark, visit the Security Roles Guide.
Fort Knox Mode / Locking Out Unfamiliar Devices
 You can further lock down your AngelTrack server by forbidding login from any computer or device that AngelTrack has not seen before.
You can further lock down your AngelTrack server by forbidding login from any computer or device that AngelTrack has not seen before.
This dramatically increases the security for your data, but also creates a minor ongoing hassle as new devices must be registered from time to time. To learn more, read the Login Mode Guide.
Securing Passwords
Password policy is a pillar of IT security. AngelTrack has many security features related to passwords; please review each one, so that you can update company policy to take advantage of them.
Password expiration
 AngelTrack has a password expiration interval, configurable on the Preferences page underneath the Settings page. By default, the expiration interval is 180 days. You can choose any interval from 1 to 999 days, or set it to 0 to disable password expiration.
AngelTrack has a password expiration interval, configurable on the Preferences page underneath the Settings page. By default, the expiration interval is 180 days. You can choose any interval from 1 to 999 days, or set it to 0 to disable password expiration.
When an employee's password is expired, they will be prompted to change it when they next access AngelTrack. As with announcements, the password expiration prompt will not be shown if the employee has an active dispatch assigned.
Password expiration has another benefit: When employees are prompted to reset their password, they are also prompted to update their mobile number, their mailing address, and their emergency contact... in case these are outdated.
If an employee enables two-factor authentication [2FA] on their account, and has a valid messaging address on file for that purpose, then AngelTrack will double their password expiration interval. For example, if the system is configured for 180-day password expiration, then anyone using 2FA on their account will only have to reset their password once every 360 days.
Common passwords automatically prohibited
 AngelTrack has a built-in list of the 150 most commonly-used passwords. Attackers have the same list, and routinely use it to conduct brute-force attacks. To protect you from such attacks, AngelTrack does not permit any employee to choose a password that is on the list.
AngelTrack has a built-in list of the 150 most commonly-used passwords. Attackers have the same list, and routinely use it to conduct brute-force attacks. To protect you from such attacks, AngelTrack does not permit any employee to choose a password that is on the list.
It also does not let them choose their name, or the company name, or any common word as their password.
Warn employees to not share their passwords
Employees should be counselled -- and then occasionally reminded -- that they are strictly prohibited from sharing passwords with other employees.
Avoiding password-sharing protects both the employee and the agency.
Password complexity settings
 You can adjust AngelTrack's password complexity requirement, by visiting the Preferences page under Settings, if you have Administrator privileges. The password settings are in the "Security" section.
You can adjust AngelTrack's password complexity requirement, by visiting the Preferences page under Settings, if you have Administrator privileges. The password settings are in the "Security" section.
You can increase the minimum password length and also the requirements for upper-case, numeric, and special characters.
Let AngelTrack choose your new password
Probably you are like most people, using the same or similar password on many different websites and online services.
The danger is, if one of those websites gets breached, and your favorite password gets exposed, the hackers will then try the same username and password on as many other websites as they can, to see if you used the same credentials elsewhere.
 For this reason it is best to let AngelTrack choose your password for you. But don't worry, it won't give you a jumble of letters, numbers, and symbols that is impossible to remember. Instead, your new password will be a string of ordinary English words separated by dots. This makes it easy to remember, and easy to type on your smartphone, but very difficult for a hacker to guess, because AngelTrack's wordlists are so large that it would take billions of attempts, which will not work against AngelTrack due to the auto-lockout feature discussed below.
For this reason it is best to let AngelTrack choose your password for you. But don't worry, it won't give you a jumble of letters, numbers, and symbols that is impossible to remember. Instead, your new password will be a string of ordinary English words separated by dots. This makes it easy to remember, and easy to type on your smartphone, but very difficult for a hacker to guess, because AngelTrack's wordlists are so large that it would take billions of attempts, which will not work against AngelTrack due to the auto-lockout feature discussed below.
Built-in defenses against account takeover
 High-level users (members of the HR and Administrator roles) have the authority to change the password of another user.
High-level users (members of the HR and Administrator roles) have the authority to change the password of another user.
Medium-level users (members of the Captain, HR, and Administrator roles) also have the authority to change another user's primary messaging address, if that other user is not a high-level user (HR or Administrator). The new primary messaging address could then be used for a self-service password reset.
Therefore, if a medium- or high-level user account became compromised, it could try to take over other similar-access accounts in order to conceal its actions.
AngelTrack protects against this by sending a notification message to the target user account if anyone ever changes its password or its primary messaging address, so that they can intervene if the change was not anticipated.
Self-service password reset
If an employee has typed their messaging address (email or SMS) into their employee file in AngelTrack, they will be able to reset their own password if locked out. In this situation, AngelTrack will offer a reset button to the employee:
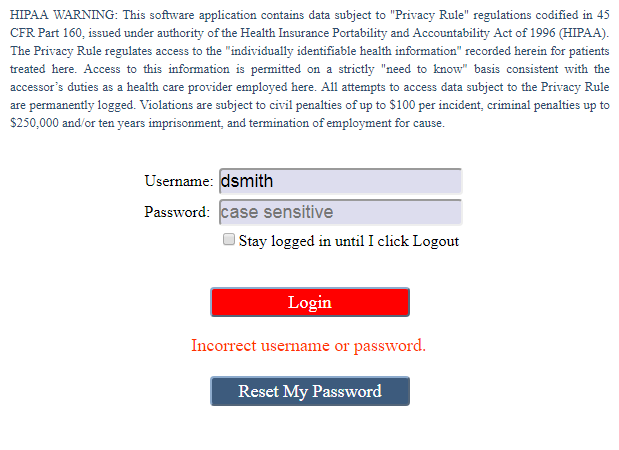
The employee will then receive a message containing a new, randomly-generated AngelTrack password.
Two-Factor Authentication / 2FA / MFA
 Every user account in AngelTrack can be enabled for two-factor authentication, as long as it has a messaging address (email or SMS) on file or has connected an authenticator app.
Every user account in AngelTrack can be enabled for two-factor authentication, as long as it has a messaging address (email or SMS) on file or has connected an authenticator app.
Any employee using 2FA on their account will enjoy twice the normal password expiration interval; for example, if all employees must reset their passwords every 180 days, then 2FA users must reset every 360 days.
You can use the Employees Missing HR Data report under HR Home to see which employees have and have not enabled 2FA on their AngelTrack accounts.
If your user account has Administrator access, be sure to enable two-factor authentication. Any user account that has Administrator access but which does not have two-factor authentication will be automatically deactivated after 90 days of inactivity.
To learn more about two-factor authentication in AngelTrack, please visit the Two Factor Authentication Guide.
Mandatory two-factor authentication
Your AngelTrack server is pre-configured to require 2FA on all accounts with any of the following roles:
- Administrator
- Human Resources
- Biller
You can change that, or mark other security roles for mandatory 2FA, by visiting the Preferences page under Settings, and scrolling down to the "Security" section.
Temporarily disabling two-factor authentication
You can disable two-factor authentication on a user account by visiting its Employee Edit page, accessed by clicking the user account in the Employees List, and unchecking the relevant box on the user's Messaging settings.
If that user belongs to any security roles for which 2FA is mandatory, AngelTrack will allow the user to login without it, but will then prompt the user to re-establish it.
Automatic Account Lockout
 In order to defend against brute-force password guessing attacks, AngelTrack automatically locks its user accounts after several unsuccessful password attempts.
In order to defend against brute-force password guessing attacks, AngelTrack automatically locks its user accounts after several unsuccessful password attempts.
This prevents an attacker from running a program all day and night to try logging in using common passwords. Here is what AngelTrack's login page will show when an account gets locked after several incorrect passwords:
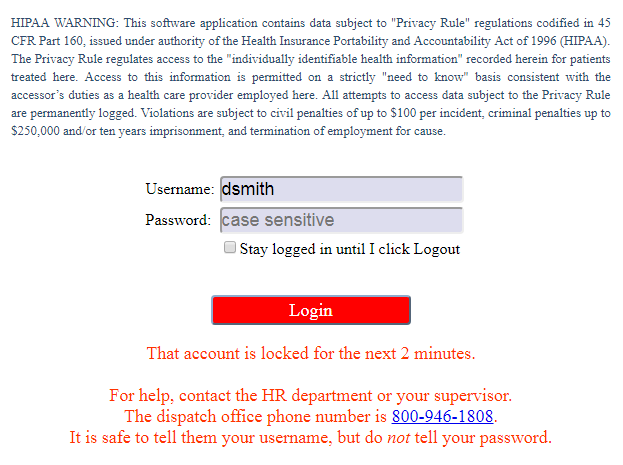
When locking a user account after repeated password failures, AngelTrack follows this lockout schedule:
| Consecutive Incorrect Passwords | Lockout Duration |
|---|---|
| 3 | 2 minutes |
| 4 | 5 minutes |
| 5 | 10 minutes |
| 6+ | 15 minutes |
A locked account can be unlocked by anyone with Captain, Lieutenant, Dispatcher, or HR privileges. Just visit the Employees List, find the locked row, and click the red "Locked" button.
'Admin' account has a harsher lockout schedule
If the user account's login name is "admin", then the lockout duration is always four hours, and the above chart does not apply. This is because it is easy for any attacker to guess that "admin" is a valid login name, and therefore the "admin" account will probably be the target of any brute-force password-guessing attack.
Automatic Defense Against Username-Guessing Attacks
 The logon page automatically defends against attempts to guess logon names, by refusing to confirm or deny whether any particular logon name is valid.
The logon page automatically defends against attempts to guess logon names, by refusing to confirm or deny whether any particular logon name is valid.
AngelTrack will even allow the attacker to attempt a self-service password reset via email, offering them a fake email address so that they cannot tell whether a logon name is valid. This is why, if you accidentally try to logon with the wrong username, you might see AngelTrack offer to send a password reset message to an email address that you don't recognize. AngelTrack won't actually send that email.
Reducing the CSRF Attack Surface
A CSRF attack is when you inadvertently visit a hostile website, and the hostile website runs code in your browser to try to forge a request to your AngelTrack server. It does this by utilizing the stored authentication ticket that AngelTrack had earlier issued to your browser.
AngelTrack's pages all have CSRF defenses (aka "antiforgery tokens") but this protection is not possible for API endpoints, of which AngelTrack has many.
To reduce the risk of CSRF attacks, you can do any and all of the following:
- Implement a URL whitelist on the company network that prevents work computers from visiting any websites other than those needed for work (see below for the list of sites needed for AngelTrack);
- Forbid the use of personally-owned computers and devices, through a combination of Provisional access and Fort Knox mode.
 Disable the "Keep me logged in" option, which you can do from the Preferences page under Settings. Once this option is disabled, employees will be logged-out as soon as they close their browser, even if they did not remember to click the "Logout" button.
Disable the "Keep me logged in" option, which you can do from the Preferences page under Settings. Once this option is disabled, employees will be logged-out as soon as they close their browser, even if they did not remember to click the "Logout" button.
The latter recommendation also reduces the attack surface exposed to credential stealers, which steal the authentication cookies stored by the browser and attempt to re-use those cookies to impersonate your employees. By disabling the "Keep me logged in" option, a credential stealer who obtains the AngelTrack authorization cookies from an employee's computer will have only a short period of time to make use of them before they expire.
Securing Desktop Computers
We strongly recommend desktop computers used by back-office staff (dispatchers, billers, and the like) have a passworded screen-saver configured to protect the computer after 5 minutes of inactivity. Back-office staff enjoy a great deal of access to AngelTrack, and there is always the risk they will go home for the night without remembering to logout of AngelTrack. The passworded screensaver secures that vulnerability.
An alternative to screen-savers is to secure the door of the dispatch office and the billing office. Install automatic door-closer mechanisms on the doors, and then install keypad doorknobs so that only authorized employees may enter. Once that's done, you could set a longer screen-saver lock on the computers inside -- perhaps thirty minutes instead of just five.
Avoid old operating systems that are no longer supported by the vendor
Upgrade your desktop computers to an operating system version that is still being supported by Microsoft or Apple, ensuring that the computer will have the latest security updates.
Windows 7 is no longer being supported by Microsoft, and so may have an escalating number of vulnerabilities. Consider immediately upgrading or replacing all Windows 7 computers.
Likewise for old web browsers, such as the venerable Internet Explorer, which has since been superseded by the Microsoft Edge browser.
Install a subscription anti-virus solution
Each desktop computer should run a subscription anti-virus solution, where the subscription enables constant updates as new threats emerge in the wild. There are even PDF-born viruses that can arrive via email, so the anti-virus solution must include an email scanning feature.
 AngelTrack will run its own virus-scan on any documents that your employees attempt to upload. However, this is signature-based anti-virus, not heuristic, so it can only detect viruses that have been identified and added to the signature databases. It is no substitute for proper anti-virus protection on your workstations, to reduce the chance that one employee might inadvertently upload an infected document to a trip in AngelTrack which a different employee might then download and view, spreading the infection.
AngelTrack will run its own virus-scan on any documents that your employees attempt to upload. However, this is signature-based anti-virus, not heuristic, so it can only detect viruses that have been identified and added to the signature databases. It is no substitute for proper anti-virus protection on your workstations, to reduce the chance that one employee might inadvertently upload an infected document to a trip in AngelTrack which a different employee might then download and view, spreading the infection.
AngelTrack also blocks the upload of all executable file types, such as programs, scripts, and shortcuts.
Subscribe to an email filtering service
Email phishing attacks are now a primary vector for fraud and malware, and they grow ever more sophisticated by means of AI. For this reason, AngelTrack LLC recommends all providers subscribe to a dedicated email filtering service -- one which includes hyperlink validation.
Protect laptops and desktops with BitLocker or equivalent
It's only a matter of time until your organization loses a laptop. Protect yourself by enabling BitLocker or other whole-disk encryption on it, so that whoever finds the laptop cannot scrape any privileged information from it.
Even your desktop computers might go astray, if your dispatch office ever gets burgled, so consider protecting them in the same way.
In any case, as soon as you activate BitLocker, SAVE THE RECOVERY KEY. You can print these recovery keys and store them in a safe, or upload them to AngelTrack as employee document attachments.
Configure web browsers for maximum privacy and security
Modern web browsers have configuration options to balance privacy and security against usability. The stricter settings are more secure, but less convenient.
For business use, your employees should be visiting only those websites necessary in the line of duty -- including insurance carriers, nursing homes, hospitals, doctor's offices, clearinghouses, medical suppliers, and perhaps your bank. All those will be compatible with your browser's strictest settings, and of course AngelTrack is too (further discussion below).
If an acceptable website doesn't work with a strictly configured browser, then you can add an exception for it within the browser.
Configure an outbound whitelist on your firewall
The computers at your headquarters should never be connecting to mysterious places on the internet. To prevent this, configure your company firewall with an outbound whitelist, containing a list of allowed services and websites. This strategy is known as "deny by default", or "zero trust".
Your whitelist might look like this:
- Allow application: ntp
- Allow application: ocsp
- Allow application: ms-updates
- Allow application: smtp / pop3 / mapi
- Allow application: ftp/sftp (only if specifically needed)
- Allow application: http/https to approved websites:
- angeltrack.com
- ^.angeltrack.com
- ^.angeltracksoftware.com
- google.com
- ^.google.com
- et cetera
An outbound whitelist like that can drastically reduce the damage that a computer virus can do in your dispatch office, since it won't be able to phone home.
See below for a list of websites needed for AngelTrack, which must be added to your outbound whitelist.
Securing Mobile Devices
Automatic screen lock
A lost or stolen tablet creates a security vulnerability, if an employee was left logged-in on its web browser when the tablet went astray. The vulnerability is magnified when the tablets are set to remember the password of its user.
To secure this vulnerability, iPads and other tablets taken into the field should be configured with a lock screen and passcode. Choose a simple passcode that every employee can remember -- perhaps the last four digits of the company's main phone number? -- and then configure tablets to delete themselves after a few unsuccessful attempts.
Many modern tablets now have a thumbprint scanner integrated into their home/lock button, making it easy for crews to unlock the device using a single gesture.
Distinctive cases
To reduce the odds that company-owned mobile devices get stolen, select a protective case that is distinctively colored or decorated, and use the same case on every company-owned device.
A bright and ugly color is best: orange, lime green, fuschia. Not only do such colors make the device unappealing to steal, but they also make it easier to find when accidentally left somewhere.
Central registration and remote wipe
Company-owned mobile devices can be registered to a central authority (e.g. iTunes), which then allows tracking and remote wipe. Do not hesitate to remote wipe a mobile device that has gone missing; if it is subsequently recovered, no EMS information was lost, as AngelTrack does not store any information on the device.
Lockdown mode
Some mobile devices offer a high-security or "lockdown" mode that configures the device for maximum privacy and security. This mode disables the conveniences and optional features that are likely channels for compromise, while allowing the device to otherwise function normally for basic tasks.
Consider activating this mode on all company-owned devices. You can then add exemptions for the AngelTrack website (which needs to GPS track your crews) plus any other websites used in the line of duty.
Securing personal mobile devices
If you permit your employees to use their personal mobile devices in the line of duty, then announce a HIPAA rule which they must follow:
If you use your personal mobile device to photograph HIPAA-protected patient documents, then federal law requires you to set a password on your device. Configure the device to wipe itself after ten unsuccessful password attempts.
At the end of each shift, after all reports are sent to QA, delete all HIPAA-protected photographs from your device.
This policy is already written for you as a built-in announcement in AngelTrack; you must simply activate the announcement.
Tracking of Employee HIPAA Training
AngelTrack has a built-in certificate type to track each employee's HIPAA training, and you can add custom certificate types to track other forms of recurring training... even something as simple as a ten-minute annual update on company policy regarding AngelTrack usage.
By means of these certificate types, you can use the Crew Certificates Overview report to easily monitor which employees need a refresher course on security-related topics.
Employee Termination Policy
When an employee is terminated, it is important to immediately suspend their access to AngelTrack. Although AngelTrack does not permit gross damage like report and document deletion, a disgruntled employee could nevertheless alter his or her run reports so as to cause problems in Billing, or alter the reports crewmates to add profanity and the like. Therefore it is important to add the task "Revoke the employee's AngelTrack access" to your termination procedure.
Revoking AngelTrack access is easy. Any user with HR privileges can mark any employee inactive, which immediately suspends all AngelTrack access. Employees can easily be reactivated later, so do not hesitate to deactivate an employee when termination is imminent.
Automatic warning of stale user accounts
 When a user account has not been utilized during the past 45 days, AngelTrack automatically marks it with a ☠ skull and crossbones in the Employee List. The account will also be reported in the "Stale Employee Records" dashboard under HR Home.
When a user account has not been utilized during the past 45 days, AngelTrack automatically marks it with a ☠ skull and crossbones in the Employee List. The account will also be reported in the "Stale Employee Records" dashboard under HR Home.
It is prudent to deactivate all stale user accounts, unless you know of a specific reason to keep them active.
Logging of AngelTrack Activity
 You are already familiar with AngelTrack's journals, which track field-by-field changes to all dispatches, invoices, and timeclock entries. These journals cannot be altered or deleted by anyone, and hence are admissible in court as evidence.
You are already familiar with AngelTrack's journals, which track field-by-field changes to all dispatches, invoices, and timeclock entries. These journals cannot be altered or deleted by anyone, and hence are admissible in court as evidence.
There is also a journal of employee logon attempts and successes, available under HR Home and from each employee's Employee Self-Edit page.
In addition to these, AngelTrack keeps logs of all web activity at the request level. This means you can review who accessed your AngelTrack cloud server, including the date and time, their IP address, their device type, and the pages accessed. The log cannot be altered and is retained for a period of time specified in the Data Lifetime and Export policy.
To learn how to use AngelTrack's logs and other forensics features to trace a data leak or other malfeasance to the responsible employee, read the Data Leak Forensics Guide.
Live monitoring of connected users
 Found under the Settings page, the Heartbeat feature allows you to monitor all active connections to your AngelTrack server, including IP addresses and summaries of each connection's previous two minutes of activity. You can click each IP address to geolocate it, which gives an approximate physical location plus the name of the ISP.
Found under the Settings page, the Heartbeat feature allows you to monitor all active connections to your AngelTrack server, including IP addresses and summaries of each connection's previous two minutes of activity. You can click each IP address to geolocate it, which gives an approximate physical location plus the name of the ISP.
To learn more about the Heartbeat page and all the data it shows, please visit the Heartbeat Guide.
Data Watermarking
 AngelTrack's .PDF, .CSV, and .XML exports are all watermarked in different ways, to indicate the date and identity of the person who generated the data.
AngelTrack's .PDF, .CSV, and .XML exports are all watermarked in different ways, to indicate the date and identity of the person who generated the data.
Furthermore, AngelTrack's NEMSIS uploads are watermarked in a special way to indicate whom they were uploaded to, in case they later leak and a blamestorm begins. To learn more, refer to the Data Leak Forensics Guide.
Exfiltration Tripwire / Exfil Monitoring
 AngelTrack has a data exfiltration monitor, that will alert you whenever a large number of PHI-containing records are viewed or exported during a single day.
AngelTrack has a data exfiltration monitor, that will alert you whenever a large number of PHI-containing records are viewed or exported during a single day.
A default tripwire threshold is already set for you, but there is no one-size-fits-all setting, so you must change it to match the pace of your operation. You can modify the tripwire by visiting the Preferences page under Settings and scrolling down to the bottom.
If the tripwire activates, AngelTrack will send an alert message to all employees for which all of the following are true:
- Their account is active;
- They have a secondary-messaging email address configured; and
- They are Administrator or Principal.
The exfiltration alert will include a chart of all employees who viewed or exported at least 30 records containing PHI at any point during the day so far. Viewing or downloading a full PCR run report or a full PCR NEMSIS XML counts as 5 records.
To access the exfiltration monitor, or to adjust the tripwire, please visit the Exfiltration Monitoring Guide.
Multi-Tier Backup Schedule with Offsiting
 AngelTrack's present storage and backup parameters for your data are as follows. These parameters exceed the minimums specified in AngelTrack's Terms of Service, and therefore are subject to change without notice, at the sole discretion of AngelTrack LLC.
AngelTrack's present storage and backup parameters for your data are as follows. These parameters exceed the minimums specified in AngelTrack's Terms of Service, and therefore are subject to change without notice, at the sole discretion of AngelTrack LLC.
- 100% of customer data* lives in an SQL cluster on a RAID-10 SAN in AngelTrack's secure datacenter. Customer data is automatically pruned of expired items, per the Data Lifetime Policy.
- Customer data is backed-up at least once every three hours to a different RAID-10 SAN, where it is at rest. These backups are retained for at least 7 days.
- The backups are re-backed-up at least once every 24 hours to an offsite data preservation facility administered by Rackspace, which retains them encrypted for at least 14 days.
*Does not include raw webserver logs.
Defenses Against Ransomware
All of your data lives in AngelTrack's SQL cluster, therefore AngelTrack must defend against two kinds of ransomware attack:
Fast-moving ransomware: A malicious program gains access to SQL Server, shuts it down, and encrypts every database's files.
The defense against fast-moving ransomware is regular backups with offsiting. AngelTrack's backup system is discussed just above. If a fast-moving ransomware were to strike, probably just one day's worth of data will be lost, plus the downtime necessary to restore backups and recover.
Slow-moving ransomware: A malicious program gains access to SQL Server, and slowly encrypts individual database records across a span of months, in order to corrupt the entire backup history.
 The defense against slow-moving ransomware consists of long backup retention periods plus tripwires within the databases to discover ongoing corruption before it overtakes all retained backups.
The defense against slow-moving ransomware consists of long backup retention periods plus tripwires within the databases to discover ongoing corruption before it overtakes all retained backups.
The nature and sensitivity of AngelTrack's ransomware tripwires is a secret... but we wanted you to know that we have thought about the problem and built defenses against it. If your compliance process requires you to know exactly how it works, the information is available under NDA.
Other Security Features
To further protect your organization, AngelTrack implements the following additional security measures...
Rackspace hosting / SOC 2 data center
 AngelTrack LLC does not attempt to save money on hosting. We host exclusively on dedicated hardware at Rackspace.
AngelTrack LLC does not attempt to save money on hosting. We host exclusively on dedicated hardware at Rackspace.
Rackspace datacenters are expensive, but they are SOC 2 and FedRAMP audited with physical access control and quadruple-redundant connectivity. If you would like to see the SOC3 documents that cover your AngelTrack server, they are available from AngelTrack LLC if you will sign an NDA.
TLS v1.2 and v1.3 / SHA-256 / RSA-2048 / PQC
 Your AngelTrack server requires your computer to connect by means of the secure TLS v1.2 or v1.3 protocol. This protects all of your internet traffic from eavesdropping.
Your AngelTrack server requires your computer to connect by means of the secure TLS v1.2 or v1.3 protocol. This protects all of your internet traffic from eavesdropping.
Obsolete versions of TLS -- v1.0 and v1.1 -- are forbidden from connecting to AngelTrack, as is plain (unencrypted) HTTP. Consequently, very old mobile devices and very old desktop computers may be unable to connect, if they only support the insecure older versions of the internet protocols.
AngelTrack uses the following encryption standards:
- The SHA-256 algorithm for hashing;
- The AES-256 cipher for symmetric encryption; and
- The RSA-2048 algorithm for asymmetric encryption.
These key sizes are presently sufficient for post-quantum cryptography [PQC].
RSA will probably be the next to become obsolete; we will migrate away from it as soon as the web browser ecosystem has adopted widespread support for its replacement.
One-way password storage
Your user passwords are stored only as hashes, never in plaintext. Therefore all password authentication for your users is by one-way hash with at least 100,000 iterations.
Your integration passwords -- which AngelTrack uses to interact with other web services on your behalf, such as your clearinghouse, and your state trauma registry -- must be stored plaintext so that AngelTrack can retrieve and use them.
Immunity to password timing attacks
 AngelTrack uses -- and has always used -- SlowEquals() for password verifications, making it immune to timing attacks. It is impossible for an attacker to sample the response times of the login page to tease out the length of a user's password, since the response time does not depend on the length or the hash of the correct password.
AngelTrack uses -- and has always used -- SlowEquals() for password verifications, making it immune to timing attacks. It is impossible for an attacker to sample the response times of the login page to tease out the length of a user's password, since the response time does not depend on the length or the hash of the correct password.
Redundant domains + Redundant SSL certificates
Every AngelTrack server belongs to two different internet domains:
- angeltrack.com
- angeltracksoftware.com
The domains are served from different DNS server clusters, and each has its own independent SSL certificate. Therefore if anything goes wrong with one of the domains, or with its SSL certificate, you can still connect to your AngelTrack server via the other domain. For example if a DNS problem makes your server acme.angeltrack.com unreachable, then you can connect to it instead via acme.angeltracksoftware.com.
OV SSL certificate + HSTS preload
 AngelTrack's SSL certificate, upon which the security of your connection depends, is a high-security Organization Validation (OV) certificate with a very string 2048-bit RSA key. If you check the SSL certificate that your browser is using to connect to AngelTrack, you can see the guarantee that it was issued to AngelTrack LLC, and not just a random website claiming to be angeltrack.com or angeltracksoftware.com.
AngelTrack's SSL certificate, upon which the security of your connection depends, is a high-security Organization Validation (OV) certificate with a very string 2048-bit RSA key. If you check the SSL certificate that your browser is using to connect to AngelTrack, you can see the guarantee that it was issued to AngelTrack LLC, and not just a random website claiming to be angeltrack.com or angeltracksoftware.com.
Furthermore, our domain is registered for HSTS preload, which protects your users from man-in-the-middle attacks when using public wifi access points.
No content-delivery network / No third-party hosting
 AngelTrack is contained entirely within its own dedicated server cluster -- excepting the Google Maps in-page mapping widget and the Stripe in-page card payment widget.
AngelTrack is contained entirely within its own dedicated server cluster -- excepting the Google Maps in-page mapping widget and the Stripe in-page card payment widget.
No AngelTrack code or data is ever stored in, or served from, a content-delivery network [CDN] or any other third-party server cluster. Content-delivery networks are third-party server clusters often used by web applications to serve code data on their behalf, but which could become an attack vector at any time, as happened with the Polyfill CDN.
Thus, if you use a web-access whitelist (aka an outbound whitelist) and wish to add AngelTrack to it, you need only add these entries:
- angeltrack.com, include subdomains or else list your AngelTrack server explicitly.
- angeltracksoftware.com, include subdomains or else list your AngelTrack server explicitly. This domain is optional; it is your AngelTrack server's alternate DNS name.
- stripe.com and subdomains, used for AngelTrack licensing, for the customer self-pay portal, and for MOTO charge processing if enabled.
- maps.googleapis.com, used for the Google Maps in-page widgets.
No data off-siting / No Snowflake copies
 We never copy your data onto third-party servers for analysis, as happened with the AT&T / Snowflake data breach, in which AT&T copied customer data onto a Snowflake server for data-mining where it then got compromised.
We never copy your data onto third-party servers for analysis, as happened with the AT&T / Snowflake data breach, in which AT&T copied customer data onto a Snowflake server for data-mining where it then got compromised.
We might analyze your data for the sole purpose of improving the AngelTrack product, but if we do, we will do it in-situ, within the safety of our dedicated server cluster.
No advertising / No third-party cookies
 Your AngelTrack server is a 100% pure EMS and fire software application, 100% made in USA by native American citizens, containing zero advertising and zero third-party cookies.
Your AngelTrack server is a 100% pure EMS and fire software application, 100% made in USA by native American citizens, containing zero advertising and zero third-party cookies.
AngelTrack therefore is not vulnerable to the "drive-by infection" risk created by banner-ad networks.
You can configure your web browser to use its strictest privacy settings and its strictest security mode, and AngelTrack will work just fine... although mobile web browsers used by crew members in the line of duty must configure a privacy exception allowing AngelTrack to track their current location, to learn more please refer to the GPS Tracking of Crews Guide.
100% memory-safe languages
 AngelTrack is 100% written in memory-safe languages: C-Sharp and Transact-SQL running server-side, plus Javascript running client-side. These languages are resistant to the buffer-overflow vulnerabilities that so often ravage the IT world.
AngelTrack is 100% written in memory-safe languages: C-Sharp and Transact-SQL running server-side, plus Javascript running client-side. These languages are resistant to the buffer-overflow vulnerabilities that so often ravage the IT world.
Indeed there are no memory-unsafe languages anywhere in AngelTrack.
That said, half of AngelTrack runs inside Microsoft Internet Information Server [IIS] which is written in C++, not a memory-safe language.
We use VulMon to monitor the vulnerability databases for disclosures related to any element of our tech stack.
Dedicated per-customer SQL databases
 Every AngelTrack customer gets their own dedicated SQL Server database, within AngelTrack's high-availability SQL cluster, to hold all of their data. Your data is never commingled with that of other providers.
Every AngelTrack customer gets their own dedicated SQL Server database, within AngelTrack's high-availability SQL cluster, to hold all of their data. Your data is never commingled with that of other providers.
This forecloses the risk that a programming error could allow an admin user at a different company to access your data.
DNSSEC
 AngelTrack's DNS domains are protected by DNSSEC, which prevents a hacker from spoofing AngelTrack's domain records in an attempt to redirect your browser to a fake website masquerading as AngelTrack.
AngelTrack's DNS domains are protected by DNSSEC, which prevents a hacker from spoofing AngelTrack's domain records in an attempt to redirect your browser to a fake website masquerading as AngelTrack.
Whenever you connect to your AngelTrack server, you can be confident that it's the real thing.
We own all similar domain names
 AngelTrack LLC owns all the similar domain names, such as angeltrack.cc, angeltrack.net, angeltrack.us, angeltrack-com.com, and so forth. They are all locked down with DKIM, SPF, and DMARC, so that hackers cannot use those domains to send you phishing emails that superficially appear to be sent by AngelTrack employees.
AngelTrack LLC owns all the similar domain names, such as angeltrack.cc, angeltrack.net, angeltrack.us, angeltrack-com.com, and so forth. They are all locked down with DKIM, SPF, and DMARC, so that hackers cannot use those domains to send you phishing emails that superficially appear to be sent by AngelTrack employees.
We also own the domain names that users frequently mistype, such as "angletrack", "angeltrsck", "angeltrak", "ange1track.com", and "angeltracksoftwsre", so that a malicious actor cannot offer a website to receive visits from your crew members who mistype AngelTrack's domain name.
100% dedicated (private) hardware
 All of AngelTrack's firewalls, server blades, and SQL instances are dedicated (private) hardware in a high-availability cluster.
All of AngelTrack's firewalls, server blades, and SQL instances are dedicated (private) hardware in a high-availability cluster.
AngelTrack's SQL cluster is likewise dedicated (private) to AngelTrack LLC. It is used for no purpose other than AngelTrack.
All of AngelTrack's server blades, VMs, SANs, and SQL instances live behind our private hardware firewalls.
We do not share any hardware or virtual machines with any other application or organization.
100% high-availability [HA] deployment
 All of AngelTrack's firewalls, server blades, and SQL instances are deployed high-availability [HA]. This means there are two of everything serving each AngelTrack customer: Two firewalls, two hypervisors, two disk directors, and two SQL server VMs.
All of AngelTrack's firewalls, server blades, and SQL instances are deployed high-availability [HA]. This means there are two of everything serving each AngelTrack customer: Two firewalls, two hypervisors, two disk directors, and two SQL server VMs.
The purpose of high-availability clusters is to tolerate an unexpected failure. If any firewall, hypervisor, or disk director suffers a hardware failure, or if any SQL server instance suffers a hardware or software failure, its HA partner immediately takes over.
This is expensive. It costs nearly twice as much as a normal deployment, but it is necessary in mission-critical industries like fire and EMS.
Bug bounty program
 We run a bug bounty program to incentivize freelance security researchers to report issues to us first, so that we have time to fix them prior to public disclosure.
We run a bug bounty program to incentivize freelance security researchers to report issues to us first, so that we have time to fix them prior to public disclosure.
The bug bounty program pays cash rewards to anyone who finds and reports a security issue to us that they have found in AngelTrack, no questions asked.
Anti-Virus Scanning
 AngelTrack runs an antivirus scan on all attempted file uploads, to reduce the odds that an employee will inadvertently attach an infected document to a PCR which could then spread to other computers at your office who later view the PCR.
AngelTrack runs an antivirus scan on all attempted file uploads, to reduce the odds that an employee will inadvertently attach an infected document to a PCR which could then spread to other computers at your office who later view the PCR.
The antivirus scanner is signature-based, not heuristic, so it can only detect known viruses. It does not alleviate the need for you to run a commercial antivirus solution on all of your desktop computers, and to lock down all company-owned mobile devices.
Automatic Defenses Against Denial-of-Service Attacks
 To defend you from denial-of-service attacks, your AngelTrack server imposes limits on its network activity:
To defend you from denial-of-service attacks, your AngelTrack server imposes limits on its network activity:
- Maximum number of simultaneous connections
- Minimum client bandwidth (re: "slow loris")
- Maximum requests per client IP address per time period
- Maximum simultaneous requests per client IP address
If you have a very large headquarters where many employees simultaneously use AngelTrack via a NAT router which shares a single IPv4 address among them, you might exceed the latter two throttles. When that happens, AngelTrack will temporarily return HTTP error 403 ("Forbidden") and/or display error popups stating, "Server overload defenses are active".
To resolve this, you must upgrade your internet service to one which provides IPv6 addresses, including a router which assigns a different IPv6 address to each workstation.
Geo-Restrictions on Network Traffic
 AngelTrack denies all network traffic from the following sources:
AngelTrack denies all network traffic from the following sources:
- Any country other than USA, Canada, Mexico, Australia, and New Zealand;
- Any IP address appearing on one of several hotlists of known-malicious IP addresses; and
- Any IP address that serves as a Tor exit node.
This restriction means that offshore employees cannot access your AngelTrack server without making special arrangements. Likewise if you go on vacation to another continent. To learn more, take a look at the Georestrictions Guide.
Disclaimer
The above advice, when properly followed and implemented, will drastically reduce the opportunity for a data breach, but it is not a guarantee. AngelTrack LLC accepts no liability nor responsibility that occurs from any breach that is the result of an agency's, or an agency's employees, actions.
The above does not constitute legal advice, nor is it a substitute for a cybersecurity or HIPAA compliance audit.
Furthermore, none of AngelTrack's security features can protect you against the possibility of long-term sabotage by a determined rogue employee. For that reason, and for all the reasons we cannot think of, AngelTrack LLC recommends you take advantage of AngelTrack's many data export facilities to regularly download copies of your data. Archive the copies in a private data preservation service to which only highly trusted employees have access. Remember that you could be liable to provide this data to HHS at any point in the future, even if you no longer own your business.
Disclaimer Re: AngelTrack Training Website
The aforementioned security features protect the AngelTrack server cluster and your data in it. They do not apply to the AngelTrack training website.
The training website is a free-for-all, allowing anyone to create an account and consume the content. There is no gatekeeping, because there is no valuable data on the server, apart from the list of users which includes passwords and email addresses.
Furthermore the training website runs in Wordpress, in order to take advantage of its LMS. It is hosted at a third-party Wordpress hosting provider. AngelTrack LLC does not have Linux expertise (the AngelTrack product is built on the Microsoft stack) and so we do not attempt to administer it. At any time a vulnerability in Wordpress, or in Linux, or in the hosting provider's configuration, might be found, which could result in the disclosure of its user list. If that happens, your username, email address, and password might be leaked.
For that reason, please do not re-use a common password when you register. Select a unique password that has no value elsewhere. You are also welcome to register under an alias.


